Electrical Isolation and Protocol Security Enhancement for Remote Control Interface of High Voltage Power Supply
Remote control of high voltage power supplies enables integration with automated systems. The control interface must provide reliable communication while maintaining electrical isolation. Protocol security is essential for preventing unauthorized access and ensuring safe operation. Understanding the isolation and security requirements enables development of robust remote control systems.
Remote control requirements for high voltage power supplies are diverse. The power supply may be controlled from a distance. The control may be through wired or wireless connections. The control may be from a local or remote location. The interface must support the required connectivity. The interface must be reliable.
Electrical isolation requirements are critical for safety. The high voltage must be isolated from control circuits. The isolation must withstand the operating voltage. The isolation must be reliable over time. The isolation must meet safety standards. The isolation protects personnel and equipment.
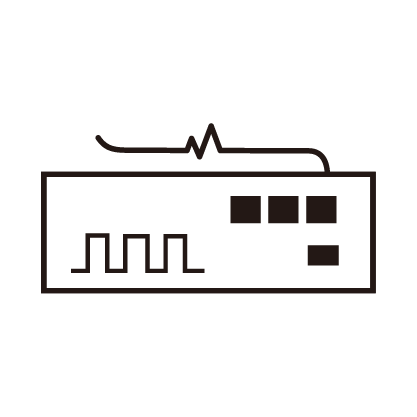
Isolation methods include several approaches. Optical isolation provides electrical separation. Transformer isolation provides galvanic separation. Capacitive isolation provides high-speed communication. The method selection depends on the requirements. The isolation must be appropriate for the application.
Optical isolation principles involve light transmission. An LED converts electrical signals to light. A photodetector converts light back to electrical signals. The light path provides electrical isolation. The isolation voltage depends on the construction. Optical isolation is widely used.
Digital isolation provides modern solutions. Digital isolators use various technologies. The isolators provide high-speed communication. The isolation is integrated in small packages. The digital isolators are reliable. The digital approach is convenient.
Communication protocols for remote control include several options. Serial protocols include RS-232 and RS-485. Ethernet provides network connectivity. USB provides computer connectivity. Wireless protocols provide flexibility. The protocol selection depends on the application.
Protocol security requirements are increasingly important. The power supply must be protected from unauthorized access. The control must be authenticated. The data must be encrypted. The security must be appropriate for the risk. The security must be maintained.
Authentication prevents unauthorized access. The user must prove identity. Passwords provide basic authentication. Certificates provide stronger authentication. Multi-factor authentication provides highest security. The authentication must be appropriate.
Encryption protects data confidentiality. The communication data may contain sensitive information. Encryption prevents eavesdropping. The encryption must be strong enough. The encryption must not affect performance. The encryption must be implemented correctly.
Integrity protection prevents data modification. The communication must not be altered. Checksums detect errors. Digital signatures verify authenticity. The integrity must be maintained. The protection must be effective.
Network security considerations are important. Firewalls restrict network access. Intrusion detection monitors for attacks. Security patches address vulnerabilities. The network security must be comprehensive. The security must be maintained.
Firmware security protects the device. The firmware must be protected from modification. Secure boot verifies firmware integrity. Code signing authenticates firmware. The firmware security must be robust. The security must be maintained over the device life.
Testing of security measures is essential. Penetration testing identifies vulnerabilities. Security audits verify the implementation. The testing must be comprehensive. The vulnerabilities must be addressed. The security must be validated.
Documentation of security features is important. The security features must be documented. The configuration must be documented. The procedures must be documented. The documentation supports the security. The documentation must be maintained.