Operation State Prediction and Fault Simulation of High Voltage Power Supply Based on Digital Twin
Digital twin technology enables virtual representation of physical systems for analysis and prediction. High voltage power supplies can benefit from digital twin approaches for improved reliability and maintenance. The digital twin integrates physical data with virtual models for comprehensive monitoring. Understanding the digital twin requirements enables development of advanced monitoring systems.
Digital twin fundamentals involve virtual-physical integration. A virtual model represents the physical power supply. The model is updated with real-time data. The model enables analysis and prediction. The integration provides comprehensive insight. The digital twin supports decision making.
Benefits of digital twin for power supplies include several advantages. Improved reliability through predictive maintenance. Reduced downtime through early warning. Optimized operation through simulation. Enhanced understanding through visualization. The benefits justify the investment.
Model development for digital twin requires comprehensive characterization. Physics-based models represent the fundamental behavior. Data-driven models learn from operational data. Hybrid models combine both approaches. The model must be accurate enough. The model must be computationally practical.
Physics-based modeling approaches include several methods. Circuit models represent the electrical behavior. Thermal models represent the heat transfer. Magnetic models represent the transformer behavior. The models must be validated. The physics models provide interpretability.
Data-driven modeling approaches include machine learning. Neural networks can model complex relationships. Regression models provide simple relationships. Time-series models capture dynamics. The data-driven models require training data. The models must be validated independently.
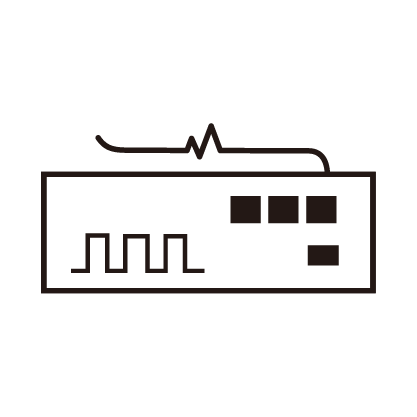
Real-time data acquisition enables model updating. Sensors measure the operational parameters. The data is transmitted to the digital twin. The update rate must be appropriate. The data quality must be adequate. The acquisition must be reliable.
State estimation determines the current condition. The model estimates internal states from measurements. The estimation accounts for measurement noise. The estimation provides insight into unmeasured quantities. The state estimation must be accurate. The estimation must be reliable.
Predictive capabilities enable proactive maintenance. Remaining useful life prediction estimates the time to failure. The prediction uses degradation models. The prediction accounts for operating conditions. The prediction enables maintenance scheduling. The prediction must be accurate enough.
Fault simulation enables what-if analysis. The model can simulate fault conditions. The simulation predicts the system response. The simulation supports fault diagnosis. The simulation enables operator training. The simulation must be realistic.
Fault injection in the model tests the detection. Various faults can be simulated. The detection algorithms can be tested. The response procedures can be validated. The fault injection improves the system. The injection must be comprehensive.
Anomaly detection identifies abnormal conditions. The model defines normal behavior. Deviations from normal indicate anomalies. The detection must be sensitive enough. The detection must not have too many false alarms. The anomaly detection must be reliable.
Visualization presents the information effectively. Dashboards show the current status. Trends show the historical behavior. Alerts indicate abnormal conditions. The visualization must be intuitive. The visualization must support decisions.
Integration with maintenance systems enables action. The predictions trigger work orders. The maintenance history updates the model. The integration must be seamless. The integration must be reliable. The integration supports the workflow.
Security considerations protect the digital twin. The data must be protected from unauthorized access. The model must be protected from tampering. The communication must be secure. The security must be comprehensive. The security must be maintained.